Invisio Bypass Shell v2.0
Backdoor Shell'Invisio Bypass Backdoor Shell v2.0' is a sophisticated PHP web shell designed for penetration testing and security auditing, enabling users to bypass standard security measures effectively. This tool is essential for ethical hacking and authorized security assessments.
Features
About Invisio Bypass Shell v2.0
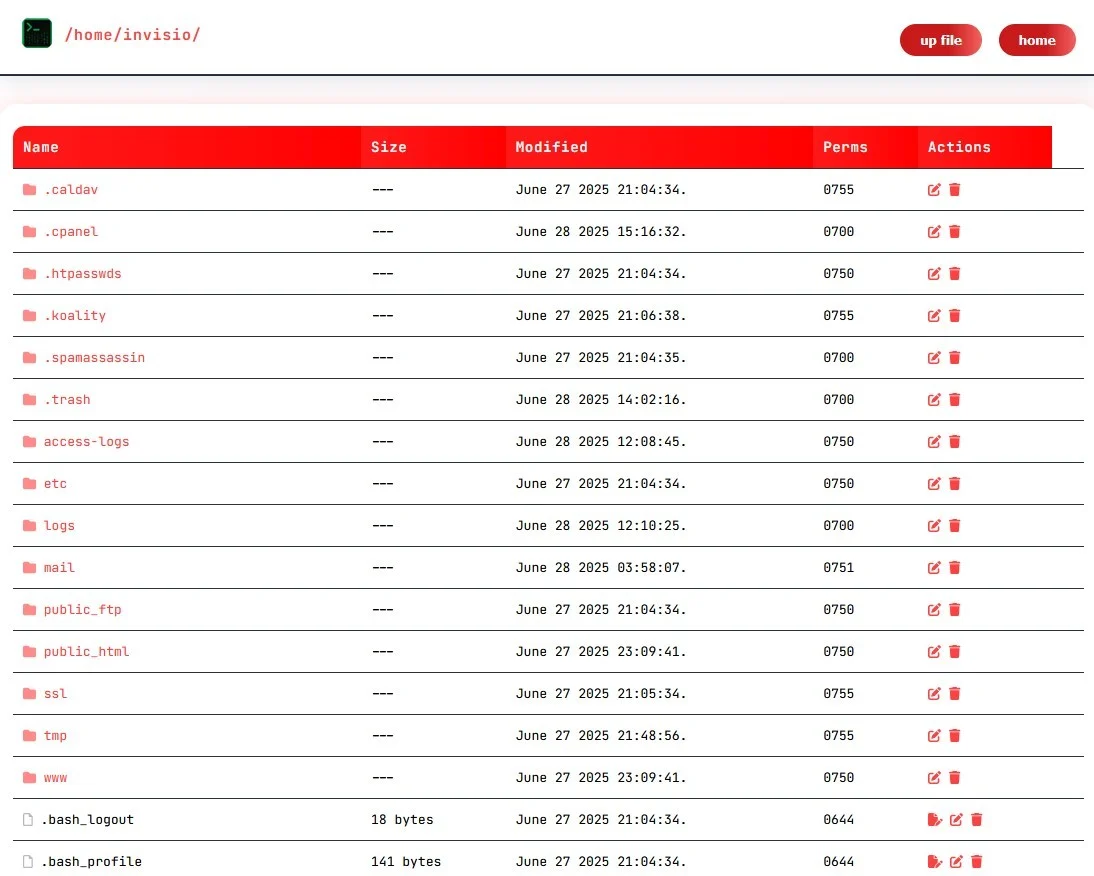
The PHP web shell tool, 'Invisio Bypass Backdoor Shell v2.0', serves as a sophisticated utility designed for penetration testing and security auditing, enabling ethical hackers to remotely manage backend servers and execute commands. This tool is particularly noted for its ability to bypass standard security protocols, thus providing a real-time testing environment for vulnerability assessment and backend server management. Crafted with an architecture that supports stealth operations, Invisio allows testers to simulate advanced cyber-attack scenarios to evaluate the robustness of network defenses. As a backdoor shell, it facilitates remote execution, offering a comprehensive testing framework for systems typically targeted in cyber-attacks. Its use in controlled environments helps organizations strengthen their defenses by identifying and addressing security weaknesses before they can be exploited maliciously. Invisio Bypass Backdoor Shell v2.0 is pivotal for professionals in the field of cybersecurity, seeking to enhance their understanding of bypass techniques and refine their skills in maintaining the integrity and security of IT infrastructures. It is imperative to note that while this tool can significantly aid in ethical hacking endeavors, its deployment should always comply with legal standards and organizational policies to avoid unauthorized access and potential misuse.
WARNING: This tool is provided for authorized security testing and educational purposes only. Deploying on systems without explicit written authorization violates applicable computer fraud laws (CFAA, CMA, StGB §202a, etc.) and may result in criminal prosecution. The user assumes full responsibility for compliance with all applicable laws.