privdayz v1 shell multi bypass tools
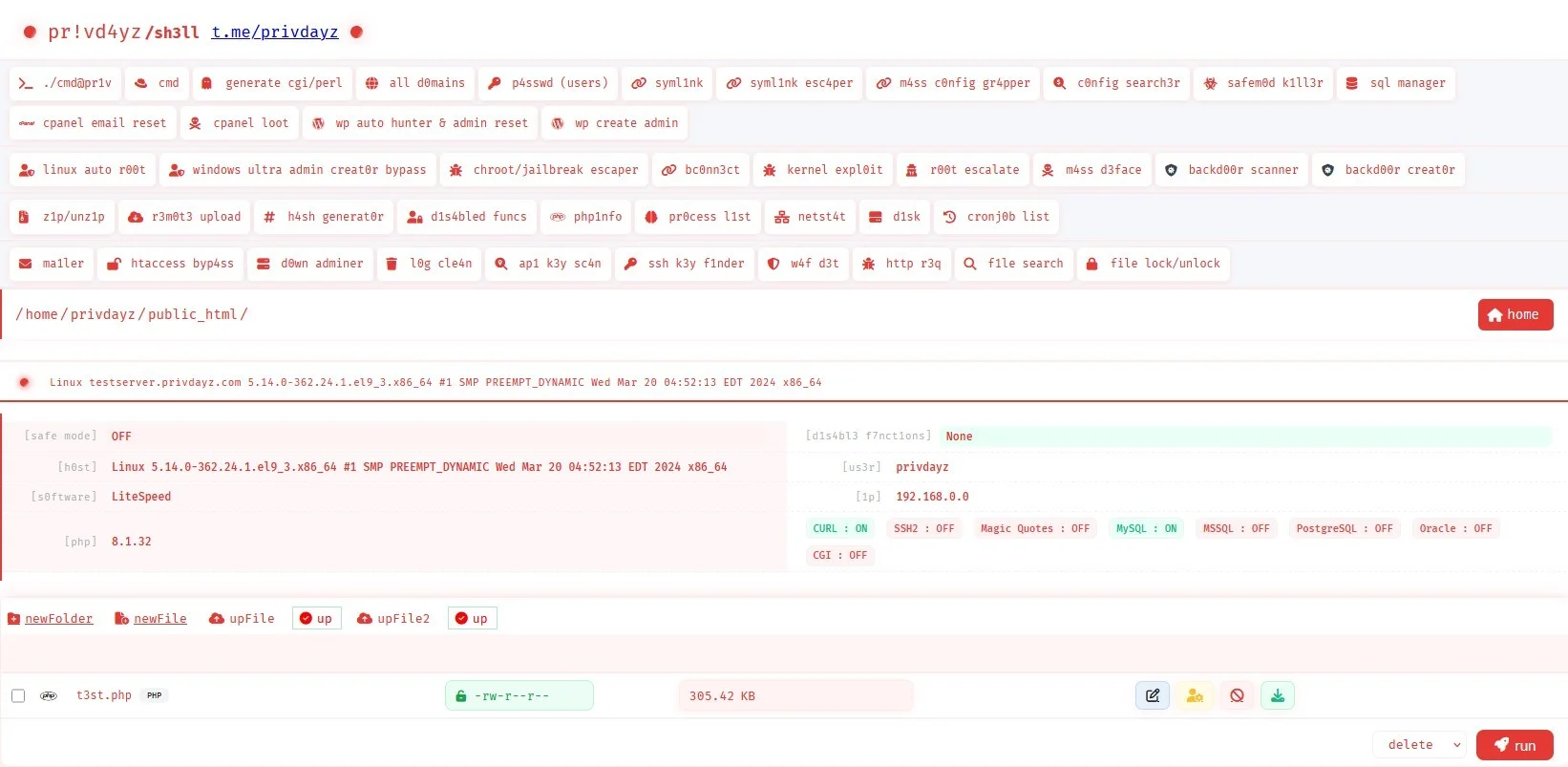
Backdoor ShellPrivdayz v1 Shell excels in advanced penetration testing and security auditing, offering features like bypass capabilities, auto-root for both Linux and Windows, and over 40 integrated tools, including symlink and CGI support.
Features
About privdayz v1 shell multi bypass tools
The Privdayz v1 shell, a PHP web shell tool, is crafted to enhance capabilities in areas such as bypass techniques, remote execution, and backend server management. This robust tool is particularly useful for penetration testing, security auditing, and ethical hacking. Designed to streamline vulnerability assessments, Privdayz v1 shell incorporates over 40 utilities including auto-root features for both Linux and Windows systems, and advanced symlink functionalities. Its architecture supports bypassing certain security measures, enabling testers to simulate sophisticated cyber-attack scenarios in a controlled environment. By integrating CGI scripts, the tool further expands its utility in testing server-side execution and interaction. The shell's comprehensive toolkit makes it a preferred choice for security professionals aiming to assess and strengthen the security posture of their IT infrastructure. It facilitates a deeper understanding of potential vulnerabilities and the impact of various attack vectors. Utilization of the Privdayz v1 shell should strictly adhere to legal and ethical standards, ensuring it is deployed only within the boundaries of authorized testing environments. By doing so, cybersecurity experts can safeguard systems against complex threats while enhancing their skills in real-world security applications.
WARNING: This tool is provided for authorized security testing and educational purposes only. Deploying on systems without explicit written authorization violates applicable computer fraud laws (CFAA, CMA, StGB §202a, etc.) and may result in criminal prosecution. The user assumes full responsibility for compliance with all applicable laws.