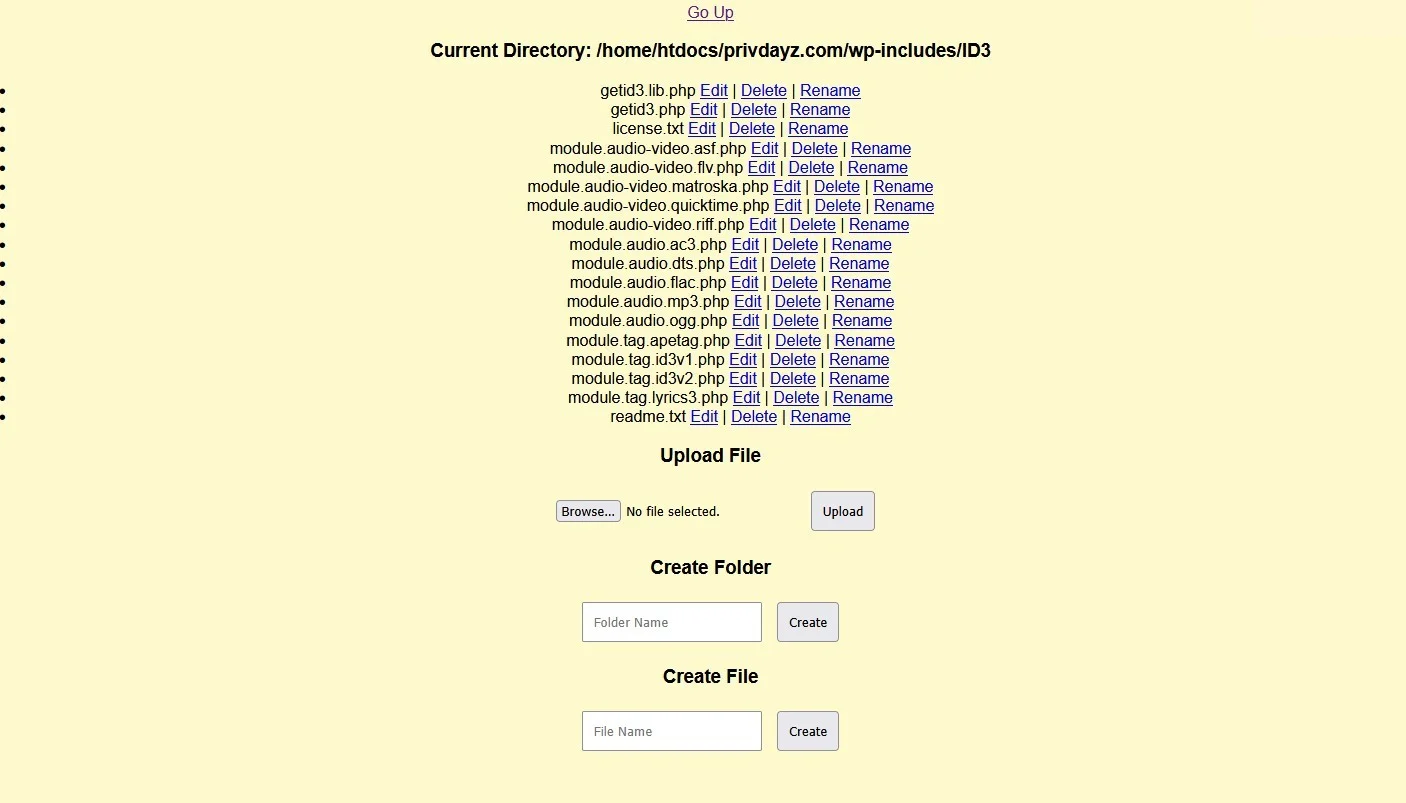
Backdoor File Manager Shell
Backdoor Shell'Backdoor File Manager Shell' is a PHP tool designed for penetration testing and security auditing, enabling users to manage files remotely and bypass standard access controls. Ideal for authorized security assessments to strengthen network defenses.
Features
About Backdoor File Manager Shell
The PHP web shell tool known as 'Backdoor File Manager Shell' is a sophisticated utility designed primarily for backend server management, enabling users to execute commands remotely for various purposes including security auditing, penetration testing, and ethical hacking. This tool facilitates direct interaction with a server's files and databases, which is critical in testing the robustness of network defenses and performing comprehensive vulnerability assessments. Embedded within its architecture are advanced bypass techniques that allow it to circumvent conventional security protocols, thereby providing an authentic environment for testers to identify potential security flaws. The application of 'Backdoor File Manager Shell' in controlled scenarios helps organizations and cybersecurity professionals understand and fortify the security posture of their systems against unauthorized access and malicious attacks. The tool’s capability for remote execution plays a pivotal role in simulating real-world attack scenarios, thereby enhancing the effectiveness of security measures and protocols. It is imperative to note that while powerful, this tool should only be used within the legal constraints and ethical guidelines that govern cybersecurity practices to ensure it serves the purpose of improving and not harming the security infrastructure.
WARNING: This tool is provided for authorized security testing and educational purposes only. Deploying on systems without explicit written authorization violates applicable computer fraud laws (CFAA, CMA, StGB §202a, etc.) and may result in criminal prosecution. The user assumes full responsibility for compliance with all applicable laws.