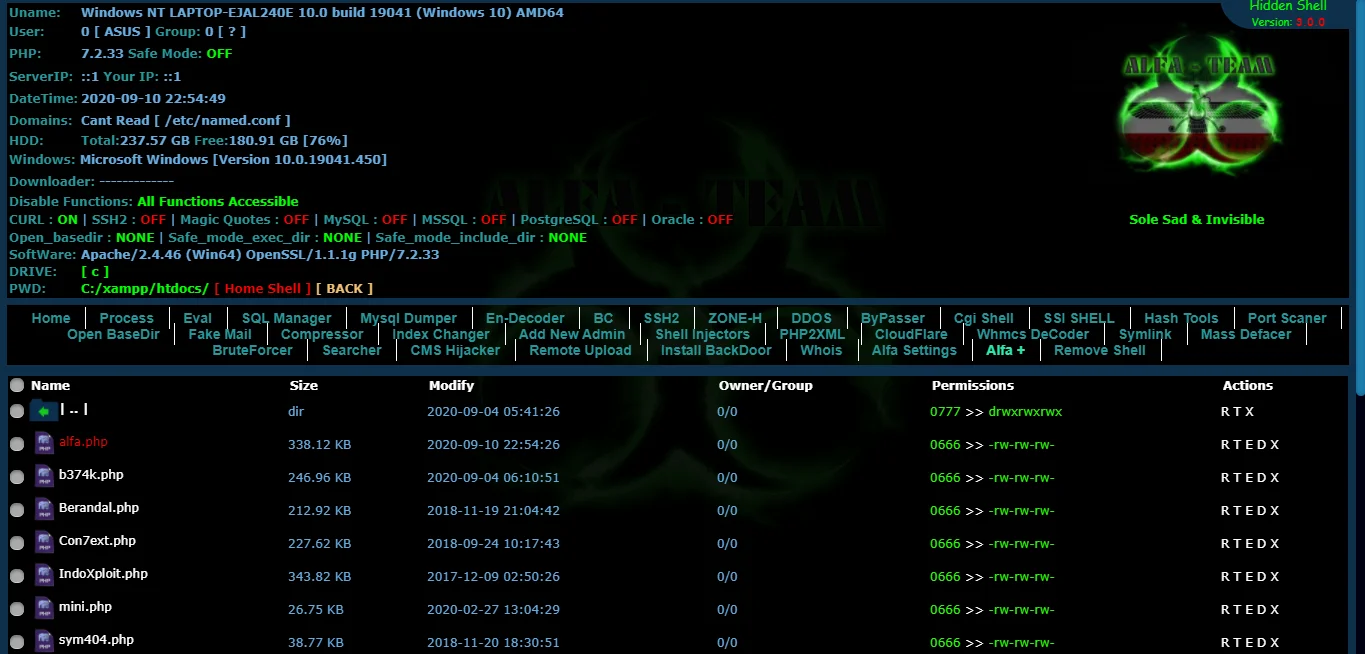
Alfa v4.0 Shell
PHP ShellAlfa v4.0 Shell is a PHP web shell designed for penetration testing and security auditing, enabling users to bypass standard access controls. This tool facilitates authorized security assessments to identify and mitigate vulnerabilities effectively.
Features
About Alfa v4.0 Shell
The PHP web shell tool 'Alfa v4.0 Shell' serves as a potent instrument for backend server management, specifically engineered to facilitate remote execution, making it a crucial asset in penetration testing and security auditing. Designed with a streamlined architecture, Alfa v4.0 enables users to execute server-side commands via a web interface, offering a practical avenue for ethical hacking and vulnerability assessment. This tool is particularly invaluable in scenarios where security professionals need to assess and enhance the defenses of web applications by simulating sophisticated cyber-attack strategies. Alfa v4.0 Shell comes equipped with various bypass techniques that help in evading common security measures, thus providing a realistic environment for testing. Its capabilities are essential for penetration testers and security experts who require a deep understanding of how attackers can exploit web applications' vulnerabilities through remote execution. Moreover, Alfa v4.0 Shell supports a range of functionalities that streamline complex tasks such as database management and file manipulation, thereby reinforcing its role in comprehensive security strategies. By integrating Alfa v4.0 Shell into their toolkit, cybersecurity professionals can ensure a thorough examination and fortification of web-based applications, making it a cornerstone in ethical hacking endeavors and the broader field of cybersecurity.
WARNING: This tool is provided for authorized security testing and educational purposes only. Deploying on systems without explicit written authorization violates applicable computer fraud laws (CFAA, CMA, StGB §202a, etc.) and may result in criminal prosecution. The user assumes full responsibility for compliance with all applicable laws.