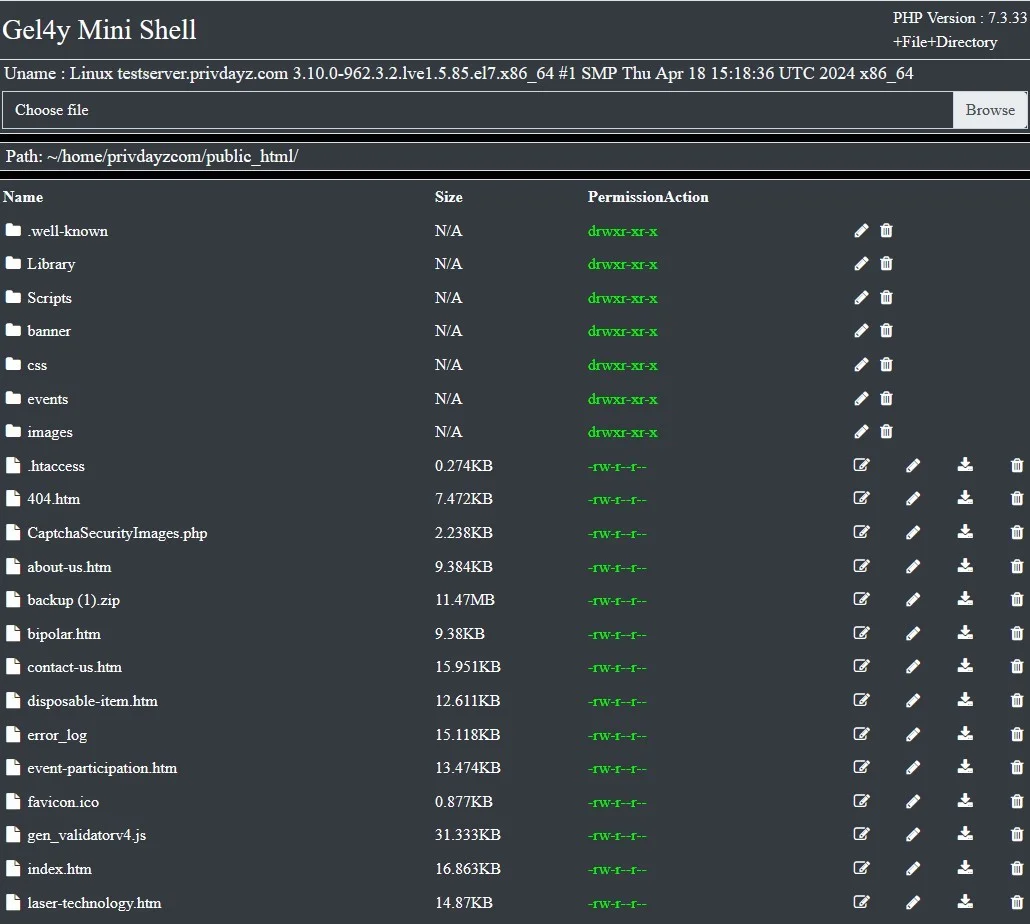
Gel4y Mini Shell
Backdoor ShellGel4y Mini Shell is a PHP-based tool designed for security auditing and penetration testing, enabling users to bypass restrictions and manage server-side operations effectively. Ideal for authorized cybersecurity assessments and enhancing server control.
Features
About Gel4y Mini Shell
The PHP web shell tool named 'Gel4y Mini Shell' serves as a potent instrument primarily utilized in penetration testing and security auditing. Engineered to facilitate backend server management, this compact yet robust shell allows ethical hackers to perform vulnerability assessments and execute commands remotely on a server, mimicking the capabilities of a more intrusive cyber attacker. By leveraging this tool, security professionals can understand how attackers exploit web applications and can implement more effective security measures. Gel4y Mini Shell incorporates various bypass techniques that help in evading simple security detections, making it an indispensable tool for testing the resilience of network defenses against web shell attacks. It is essential in scenarios where testers need to verify the effectiveness of security policies and the server's response to unauthorized remote execution attempts. Despite its utility in ethical hacking, Gel4y Mini Shell must be used with strict adherence to legal frameworks to prevent any unauthorized access which could lead to potential misuse. As such, it's crucial for users to have explicit permission for using this tool in any environment to ensure all testing is ethical and within legal boundaries. This approach not only enhances the security posture of systems but also aligns with best practices in cybersecurity, ensuring that penetration testing and vulnerability assessments are conducted responsibly and effectively.
WARNING: This tool is provided for authorized security testing and educational purposes only. Deploying on systems without explicit written authorization violates applicable computer fraud laws (CFAA, CMA, StGB §202a, etc.) and may result in criminal prosecution. The user assumes full responsibility for compliance with all applicable laws.