HOLO Backdoor Shell
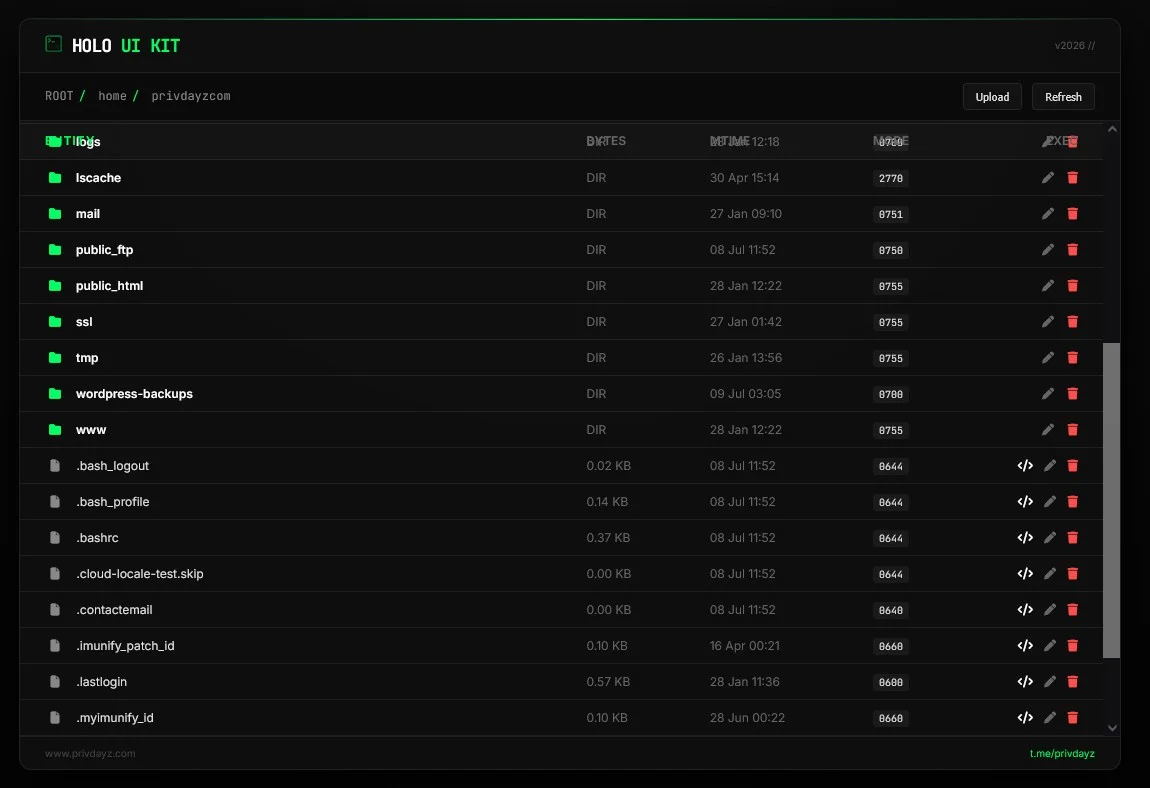
Backdoor ShellHOLO Shell, a PHP web shell designed for security auditing and penetration testing, enables discreet server interactions to bypass standard detection methods. Ideal for authorized system vulnerability assessments and educational purposes.
Features
About HOLO Backdoor Shell
The HOLO Shell, also known as Hidden JS Mini Backdoor, is a sophisticated PHP web shell tool designed primarily for backend server management and secure penetration testing. This lightweight tool enables users to execute commands on a server remotely, facilitating a streamlined process for security auditing and ethical hacking. Its architecture is crafted to maintain a minimal footprint while offering robust functionality including file management, database interaction, and executing arbitrary PHP code. What sets HOLO Shell apart is its ability to bypass common security measures subtly, making it an invaluable resource in vulnerability assessment and testing the resilience of web application defenses. The shell integrates seamlessly into existing frameworks, allowing cybersecurity professionals to simulate advanced cyber-attack scenarios to evaluate server responses. By using HOLO Shell, practitioners can uncover potential security threats and reinforce the system before actual compromise occurs. Its use in remote execution tasks provides a realistic landscape for training and development in cybersecurity defense strategies, emphasizing its application strictly within authorized and controlled environments to uphold ethical standards in cybersecurity practices. As a tool, HOLO Shell exemplifies the intersection of utility and caution, underpinning the necessity for continuous improvement and vigilance in cybersecurity efforts.
WARNING: This tool is provided for authorized security testing and educational purposes only. Deploying on systems without explicit written authorization violates applicable computer fraud laws (CFAA, CMA, StGB §202a, etc.) and may result in criminal prosecution. The user assumes full responsibility for compliance with all applicable laws.