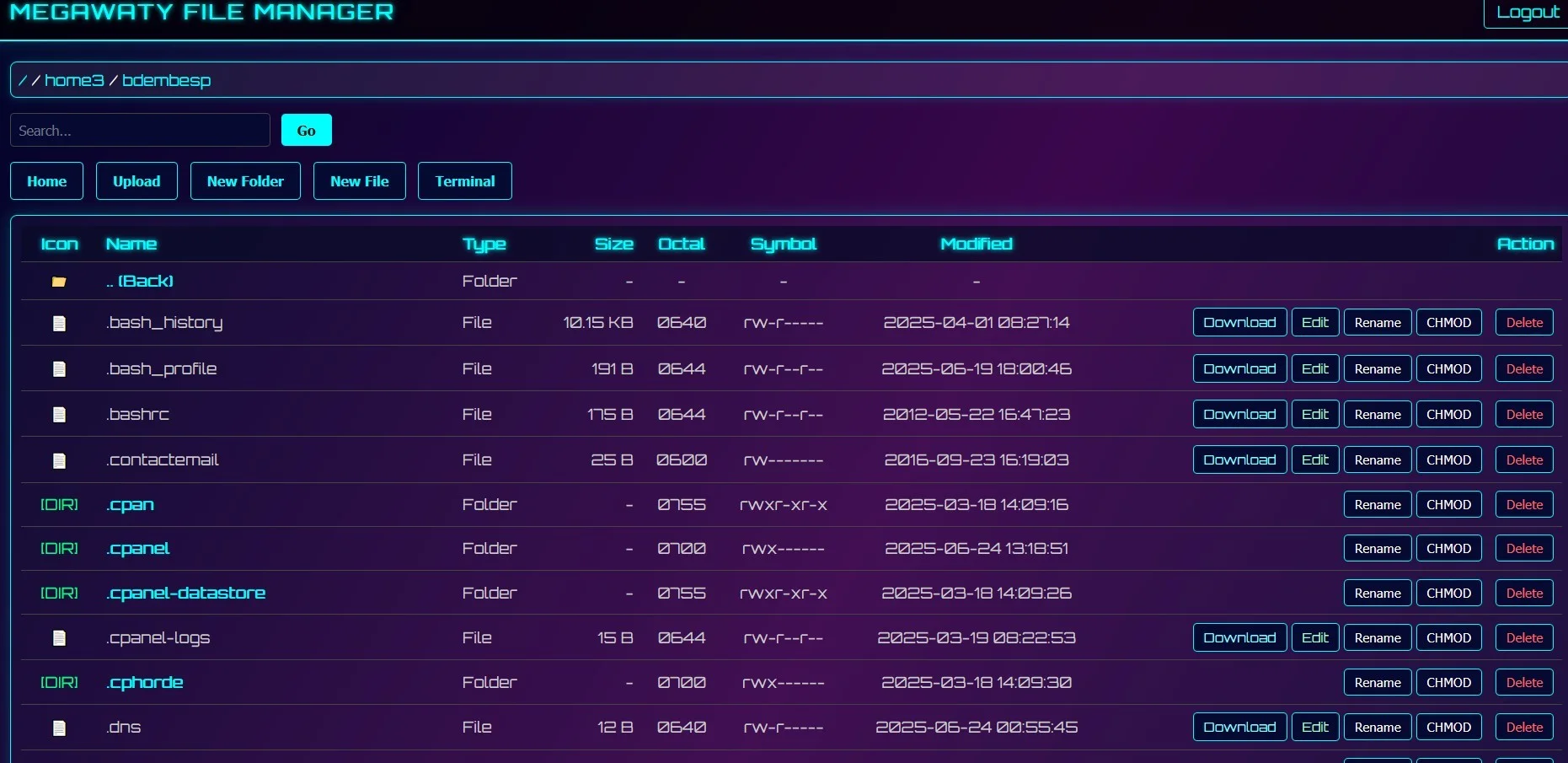
Megawaty File Manager
PHP Shell'Megawaty File Manager' is a PHP web shell tool designed for security auditing and penetration testing, enabling users to manage files remotely and bypass standard access controls in a controlled environment.
Features
About Megawaty File Manager
The Megawaty File Manager is a PHP web shell tool designed primarily for backend server management, offering comprehensive functionalities suited for security auditing, penetration testing, and ethical hacking. Crafted meticulously to assist cybersecurity professionals in managing remote servers, the tool facilitates file manipulation, database handling, and code execution, all through a streamlined web-based interface. Essential for vulnerability assessment, Megawaty File Manager incorporates advanced bypass techniques that enable testers to simulate various cyber-attack scenarios in a controlled environment, thereby identifying potential security gaps. Its capability for remote execution is particularly valuable, allowing users to execute commands on a server as if they were logged in locally, which is a critical feature for assessing the robustness of server configurations against unauthorized access. As a tool tailored for authorized testing and educational purposes, it serves as a pivotal asset in enhancing the security posture of systems by ensuring they are fortified against a spectrum of threats. By integrating Megawaty File Manager into regular security practices, organizations can better understand their exposure to vulnerabilities and refine their defense mechanisms accordingly, making it an indispensable tool in the arsenal of modern cybersecurity professionals aiming to safeguard digital assets effectively.
WARNING: This tool is provided for authorized security testing and educational purposes only. Deploying on systems without explicit written authorization violates applicable computer fraud laws (CFAA, CMA, StGB §202a, etc.) and may result in criminal prosecution. The user assumes full responsibility for compliance with all applicable laws.