AnonSec Team Backdoor Shell
Bypass Shell'AnonSec Team Backdoor Shell' is a PHP tool designed for security auditing and penetration testing, enabling users to bypass standard access controls to evaluate system vulnerabilities responsibly and effectively.
Features
About AnonSec Team Backdoor Shell
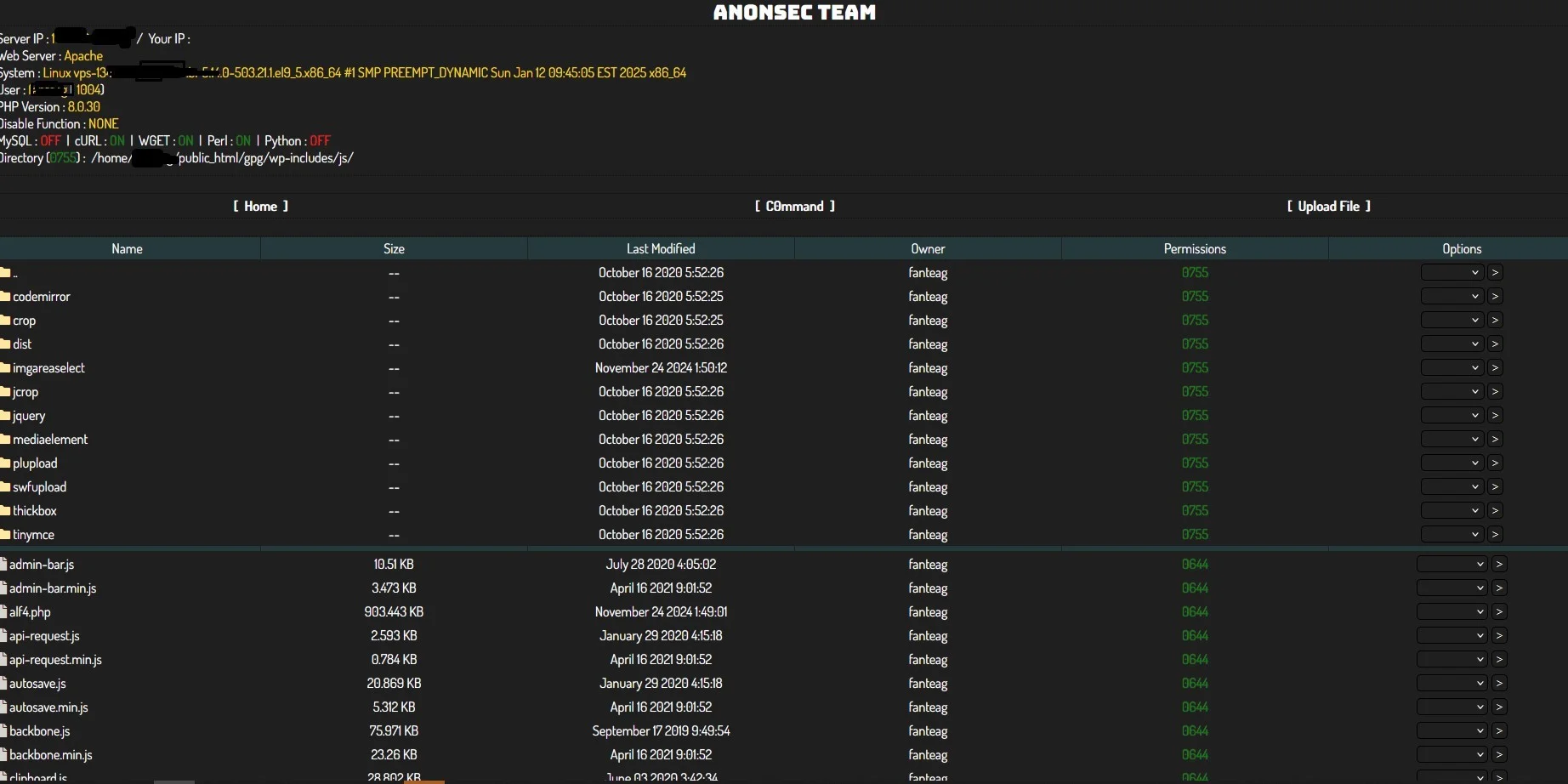
The PHP web shell tool, 'AnonSec Team Backdoor Shell', is primarily designed for backend server management and conducts security auditing by providing a remote execution interface that is accessible through web browsers. This tool's core functionality lies in its ability to execute commands on the server, making it a valuable asset in penetration testing and ethical hacking scenarios. It facilitates a comprehensive vulnerability assessment by allowing testers to simulate real-world attacks and identify potential security weaknesses. The architecture of AnonSec Team Backdoor Shell supports various bypass techniques, which help in evaluating the robustness of web application firewalls and other security measures. As part of its operation, the tool employs sophisticated mechanisms to maintain stealth while performing operations, which is crucial for testing the efficacy of intrusion detection systems and preventing false positives during security audits. Ethical hackers and security professionals utilize AnonSec Team Backdoor Shell under strict authorization to ensure that their assessments do not compromise any actual user data or infringe on privacy. By integrating this tool into their security practices, organizations can enhance their security posture significantly, as it enables them to proactively address vulnerabilities and fortify their defenses against potential threats.
WARNING: This tool is provided for authorized security testing and educational purposes only. Deploying on systems without explicit written authorization violates applicable computer fraud laws (CFAA, CMA, StGB §202a, etc.) and may result in criminal prosecution. The user assumes full responsibility for compliance with all applicable laws.