D7net Web Shell Bypass
PHP Shell'D7net Web Shell Bypass' is a specialized tool designed for penetration testing and security auditing, enabling users to test and bypass web security mechanisms effectively. This tool is integral for authorized security assessments and enhancing cybersecurity defenses.
Features
About D7net Web Shell Bypass
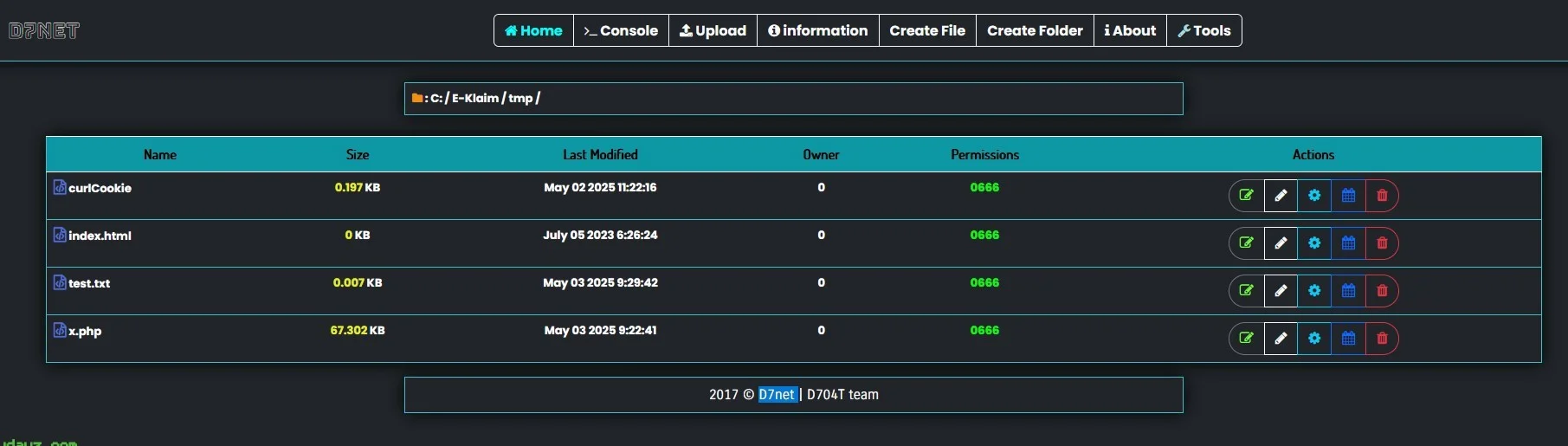
The D7net Web Shell Bypass is a specialized PHP tool designed for backend server management and remote execution, particularly useful in penetration testing scenarios where assessing the robustness of web server defenses against unauthorized access is crucial. This tool leverages advanced bypass techniques to simulate attacks, helping security professionals understand how attackers exploit vulnerabilities in web applications. The architecture of the D7net Web Shell Bypass allows it to effectively integrate into a target system, providing testers with deep insights and control over the server environment, which is essential for comprehensive security auditing. By utilizing this web shell, ethical hackers can perform vulnerability assessments and test server security by executing commands remotely, thereby identifying potential security gaps. Its usage in the realm of ethical hacking underscores its value in reinforcing cybersecurity measures and enhancing the security posture of networked systems. The D7net Web Shell Bypass, when used responsibly within the confines of authorized testing environments, serves as a crucial component in the toolkit of professionals aiming to safeguard digital assets against the ever-evolving landscape of cyber threats.
WARNING: This tool is provided for authorized security testing and educational purposes only. Deploying on systems without explicit written authorization violates applicable computer fraud laws (CFAA, CMA, StGB §202a, etc.) and may result in criminal prosecution. The user assumes full responsibility for compliance with all applicable laws.