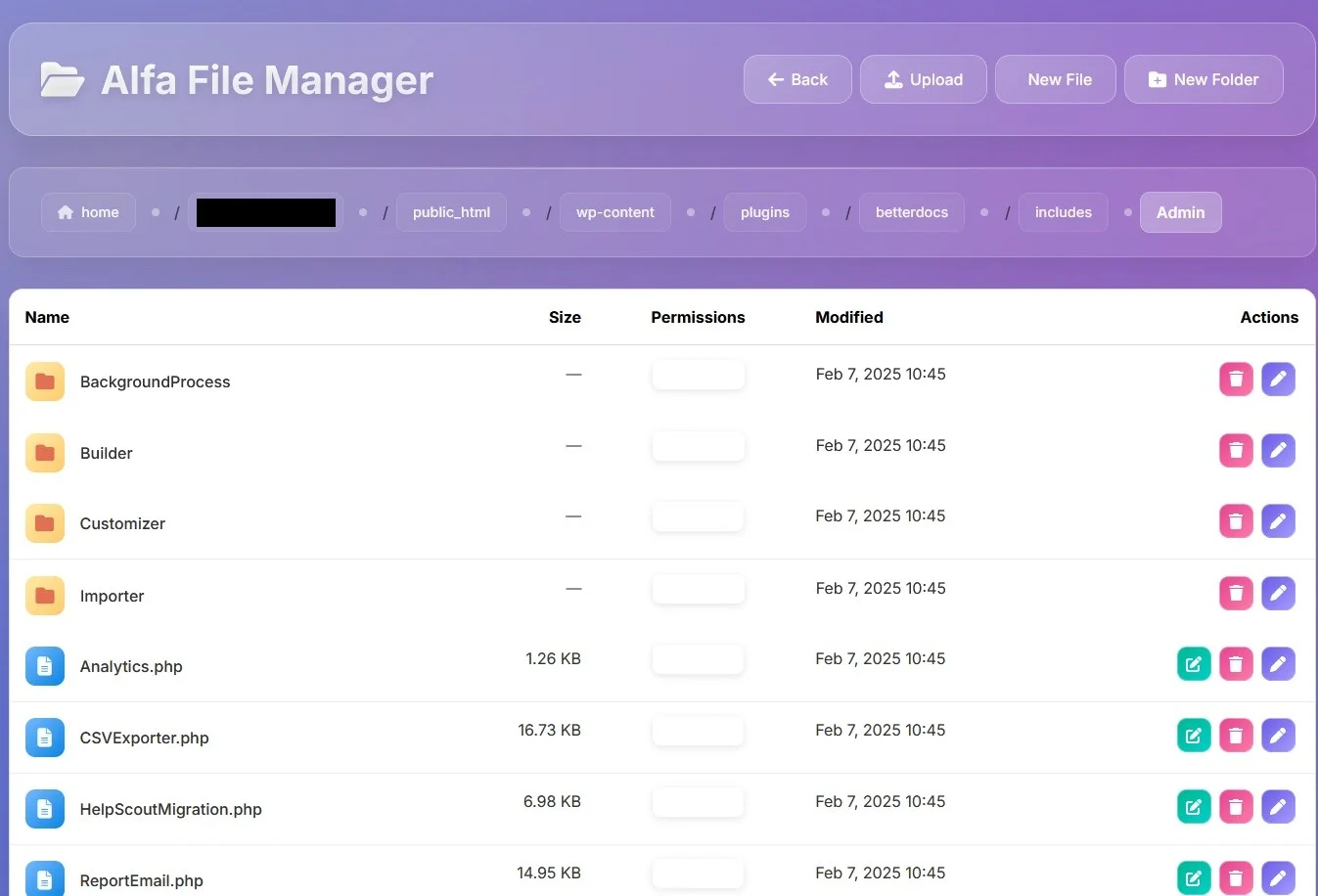
Alfa File Manager Hidden
PHP Shell'Alfa File Manager Hidden' is a PHP web shell tool designed for security auditing and penetration testing, enabling users to manage files discreetly and bypass standard access controls. Ideal for authorized cybersecurity assessments and educational purposes.
Features
About Alfa File Manager Hidden
Alfa File Manager Hidden, a specialized PHP web shell tool, enables penetration testers and cybersecurity professionals to manage files on a compromised server efficiently, providing capabilities crucial for backend server management, vulnerability assessment, and security auditing. Crafted to streamline multiple functions through a single interface, this tool is invaluable for ethical hacking, particularly in scenarios requiring discreet operations. It facilitates the remote execution of commands, effectively acting as a bridge to deeper access levels within targeted systems. The architecture of Alfa File Manager Hidden is designed to bypass standard security protocols subtly, making it an essential asset in testing environments where understanding the robustness of existing security measures against sophisticated intrusion techniques is critical. Its utility extends beyond mere file management to serve as a pivotal element in comprehensive penetration testing frameworks, allowing for an accurate simulation of cyber attacks and the assessment of potential security lapses. Ethical hackers utilize this tool to ensure that their activities remain within the bounds of authorized testing, thereby safeguarding the integrity and confidentiality of the information systems they are entrusted to protect.
WARNING: This tool is provided for authorized security testing and educational purposes only. Deploying on systems without explicit written authorization violates applicable computer fraud laws (CFAA, CMA, StGB §202a, etc.) and may result in criminal prosecution. The user assumes full responsibility for compliance with all applicable laws.