b374k Shell
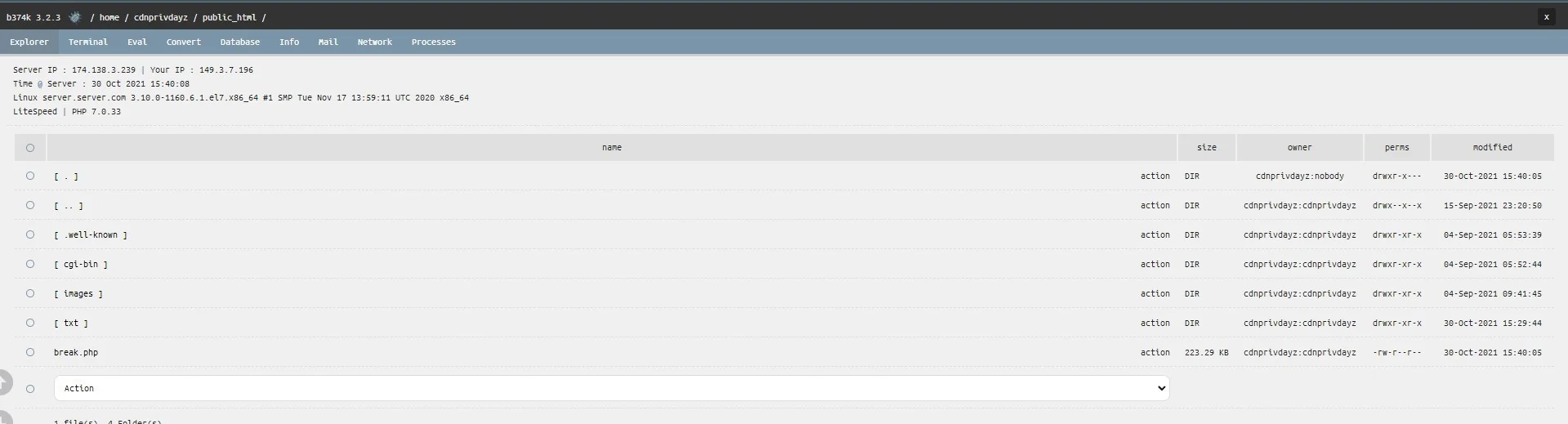
PHP ShellThe b374k Shell is a PHP web shell designed for penetration testing and security auditing, enabling users to manage remote servers and bypass standard access controls. Ideal for authorized security professionals to assess vulnerabilities effectively.
Features
About b374k Shell
The b374k Shell is a PHP-based web shell widely employed in penetration testing and ethical hacking to manage remote servers, providing an interface that supports various functions such as command execution, database management, and file handling. Crafted meticulously to facilitate backend server management, this tool enables users to execute commands on servers remotely, ideal for security professionals conducting vulnerability assessments and security auditing. Its robust design includes features that support bypass techniques, allowing testers to simulate advanced cyber-attack scenarios to identify potential security weaknesses. By integrating tools for remote execution, b374k Shell serves as a critical component in a comprehensive security framework, helping administrators and cybersecurity experts to safeguard networks against unauthorized access and potential breaches. This tool is instrumental not only in pinpointing vulnerabilities but also in demonstrating the impact of exploiting them, thereby underlining the importance of regular and thorough security practices. As with any powerful tool, it is imperative that b374k Shell is used strictly within the bounds of legal and ethical guidelines, primarily serving those involved in authorized security testing and educational purposes to enhance the security posture of digital assets efficiently and effectively.
WARNING: This tool is provided for authorized security testing and educational purposes only. Deploying on systems without explicit written authorization violates applicable computer fraud laws (CFAA, CMA, StGB §202a, etc.) and may result in criminal prosecution. The user assumes full responsibility for compliance with all applicable laws.