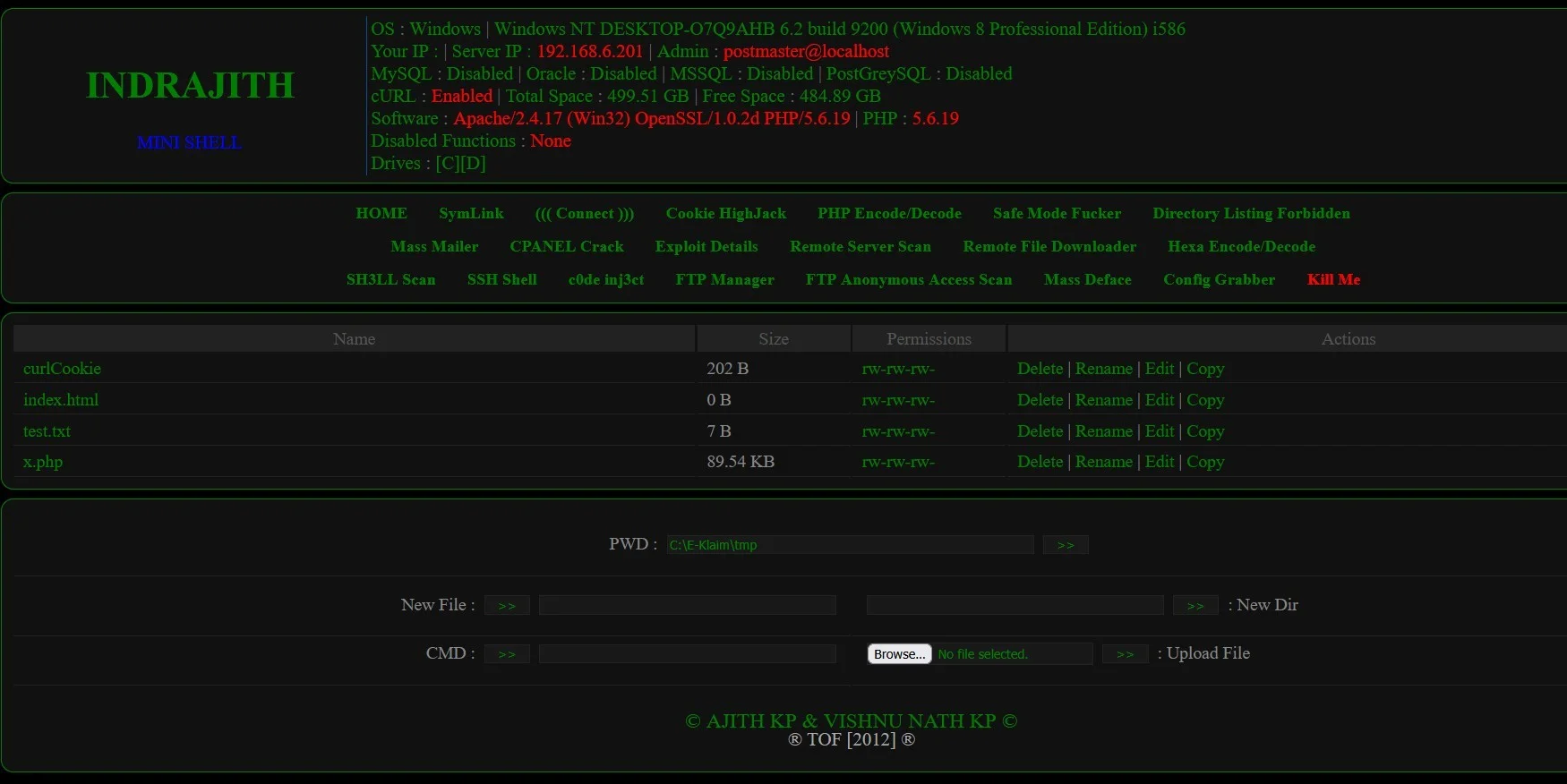
Indrajith Web Shell Symlink Bypass Tools
PHP Shell'Indrajith Web Shell Symlink Bypass Tools' is specifically designed for security professionals to enhance penetration testing and security auditing capabilities, offering advanced features to bypass symlink protections efficiently. Ideal for authorized cybersecurity assessments.
Features
About Indrajith Web Shell Symlink Bypass Tools
The Indrajith Web Shell Symlink Bypass Tool is a sophisticated PHP-based script designed for backend server management, particularly used in penetration testing and security auditing scenarios. This tool is pivotal for ethical hackers and cybersecurity enthusiasts aiming to assess the vulnerability of web servers and execute remote commands effectively. By leveraging symlink bypass techniques, the tool circumvents standard security measures, allowing testers to simulate attack scenarios and identify potential exploits in server configurations. Its architecture is tailored to facilitate a deep exploration of security layers, providing insights that are crucial for a comprehensive vulnerability assessment. Users of Indrajith Web Shell can execute a variety of server-side commands, thus gaining an understanding of the server's response to different types of security breaches. This capability is essential in refining the security posture of systems against unauthorized access and potential malicious attacks. The tool serves as a critical asset in the toolkit of professionals engaged in backend server management and ethical hacking, enabling them to perform detailed security checks and ensure that their systems are robust against various forms of cyber threats. As with any powerful tool, it should only be used within the bounds of legal and ethical guidelines to ensure that all penetration testing and remote execution activities are authorized and intended to improve cybersecurity defenses.
WARNING: This tool is provided for authorized security testing and educational purposes only. Deploying on systems without explicit written authorization violates applicable computer fraud laws (CFAA, CMA, StGB §202a, etc.) and may result in criminal prosecution. The user assumes full responsibility for compliance with all applicable laws.