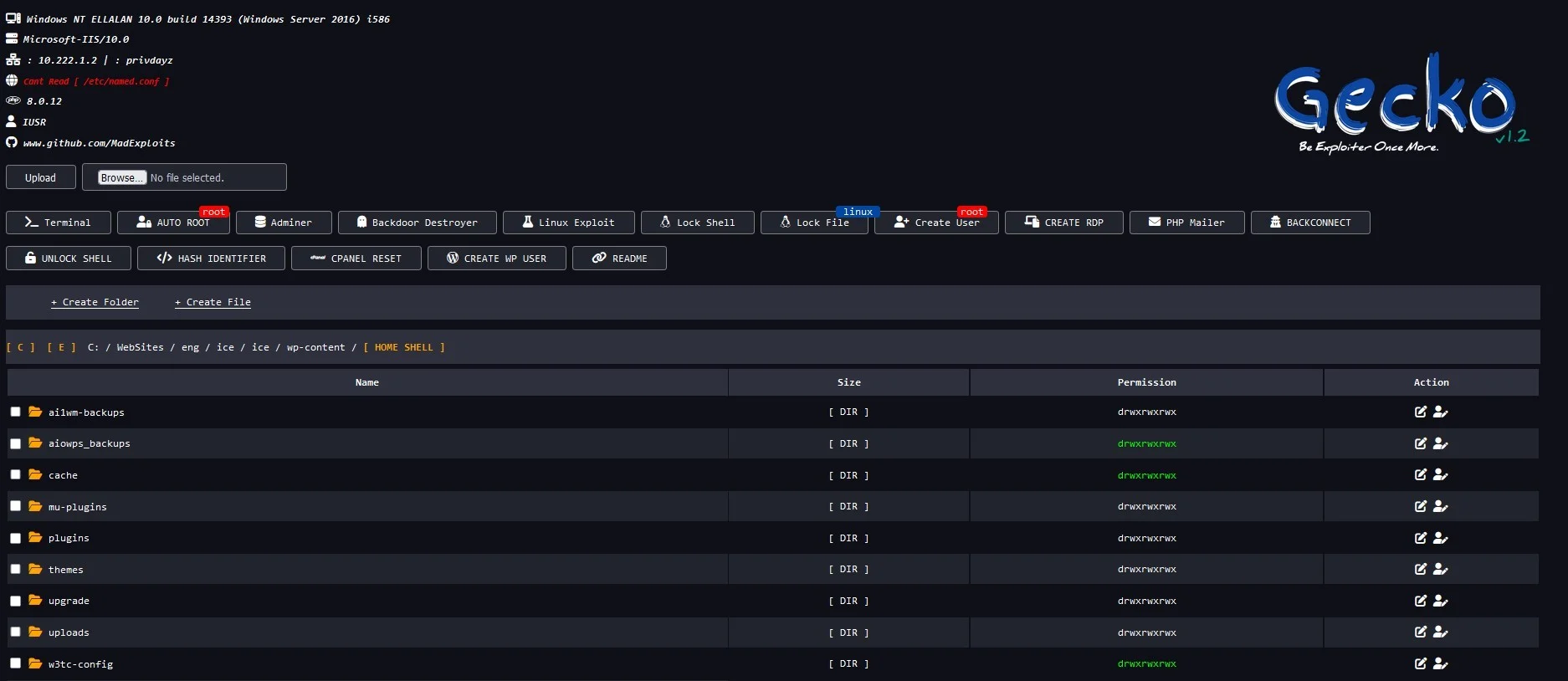
Gecko Shell Web Backdoor
PHP Shell'Gecko Shell Web Backdoor' is a robust PHP tool designed for penetration testing and security auditing, enabling users to bypass standard access controls for system evaluation. Ideal for authorized security professionals seeking to fortify web application defenses.
Features
About Gecko Shell Web Backdoor
The PHP web shell tool, 'Gecko Shell Web Backdoor,' serves as a sophisticated utility designed for backend server management, particularly useful in scenarios involving penetration testing and security auditing. This tool enables users to manage remote servers through a web-based interface, facilitating the execution of server-side commands and scripts, enhancing the efficacy of ethical hacking exercises. Gecko Shell's architecture is adept at bypass techniques which are crucial in testing the robustness of network security against unauthorized access and potential vulnerabilities. It supports various functions such as file management, database interaction, and remote execution, making it an indispensable asset in vulnerability assessment. For cybersecurity professionals engaged in ethical hacking, Gecko Shell provides a realistic environment to simulate attacks on systems, thereby helping in identifying and patching security gaps. Moreover, its utility in real-time monitoring and control during penetration testing scenarios helps in understanding the dynamic nature of cybersecurity threats and the necessary defensive maneuvers to counteract them. As such, Gecko Shell Web Backdoor epitomizes an essential tool in the arsenal of cybersecurity practitioners aiming to safeguard digital infrastructure through proactive security measures and comprehensive backend management.
WARNING: This tool is provided for authorized security testing and educational purposes only. Deploying on systems without explicit written authorization violates applicable computer fraud laws (CFAA, CMA, StGB §202a, etc.) and may result in criminal prosecution. The user assumes full responsibility for compliance with all applicable laws.