Russian File Manager Shell
Bypass Shell'Russian File Manager Shell' is a PHP-based tool designed for penetration testing and security auditing, enabling users to bypass standard access controls to simulate cyber-attack scenarios. It is essential for authorized testing and educational purposes only.
Features
About Russian File Manager Shell
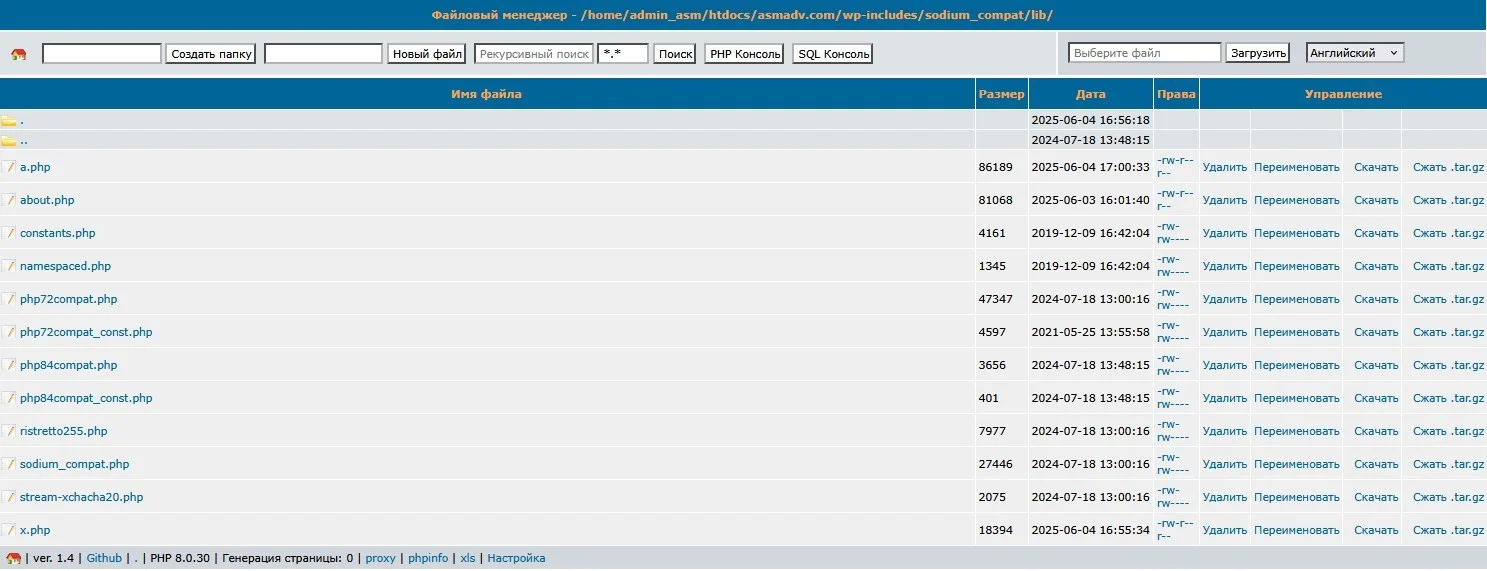
The Russian File Manager Shell is a sophisticated PHP web shell tool primarily used for backend server management and security auditing in authorized penetration testing scenarios. Designed to facilitate seamless remote execution and file management, this tool is integral for ethical hackers aiming to assess vulnerabilities within server architectures. Its functionality extends to executing commands directly on the server, providing an interface that bypasses traditional access controls, which is crucial for simulating advanced cyber-attack scenarios during vulnerability assessments. Ethical hackers frequently utilize such tools to understand and strengthen the defenses of systems against unauthorized access and potential security threats. The Russian File Manager Shell also serves as a practical resource in understanding the intricacies of bypass techniques, allowing security professionals to refine their strategies in safeguarding digital infrastructures. Its use in ethical hacking is aligned with legal and professional standards, ensuring that all penetration testing is conducted within the ethical boundaries and consented frameworks. The tool's architecture supports comprehensive backend management tasks, making it an indispensable asset for cybersecurity experts engaged in meticulous security audits and proactive threat identification. Such capabilities underscore its value in the continuous effort to fortify cybersecurity measures and train professionals in the field of information security.
WARNING: This tool is provided for authorized security testing and educational purposes only. Deploying on systems without explicit written authorization violates applicable computer fraud laws (CFAA, CMA, StGB §202a, etc.) and may result in criminal prosecution. The user assumes full responsibility for compliance with all applicable laws.