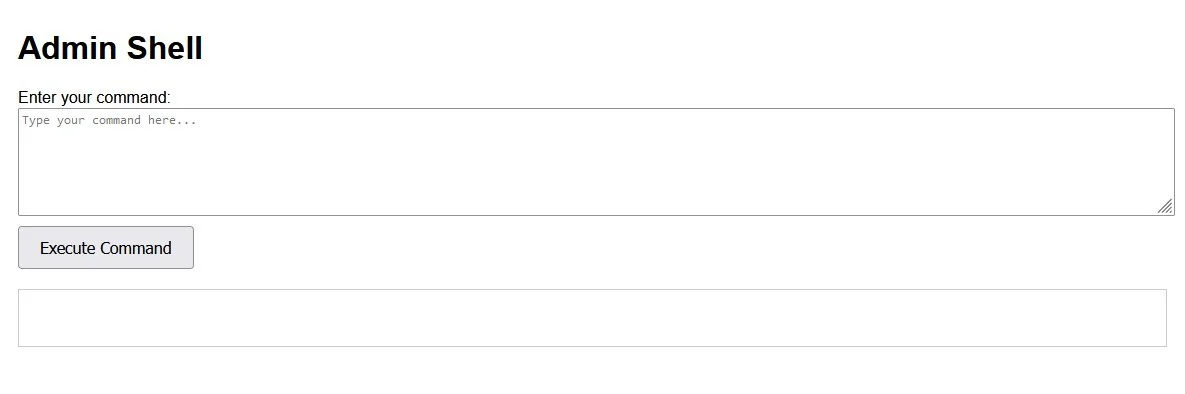
Admin Shell Backdoor Command
PHP Shell'Admin Shell Backdoor Command' is a PHP web shell tool designed for effective penetration testing and security auditing, enabling users to bypass standard access controls and simulate advanced cyber threats in controlled environments.
Features
About Admin Shell Backdoor Command
The PHP web shell tool named 'Admin Shell Backdoor Command' serves as a potent instrument for penetration testing and security auditing, primarily designed to facilitate backend server management and ethical hacking through remote execution capabilities. This tool allows cybersecurity professionals to assess vulnerabilities in web applications by simulating how an attacker might gain unauthorized access using bypass techniques. Its architecture is streamlined for ease of use in controlled environments, enabling testers to execute commands directly on the server, thus mimicking real-world attack scenarios responsibly. The 'Admin Shell Backdoor Command' is pivotal for comprehensive vulnerability assessments, offering insights into potential security lapses that could be exploited maliciously. By integrating this tool into regular security practices, organizations can enhance their defenses against sophisticated cyber threats. This tool is strictly intended for use within legal and ethical boundaries, emphasizing its role in reinforcing cybersecurity measures rather than undermining them. For those involved in developing and refining cybersecurity strategies, understanding and utilizing such tools can be crucial for advancing their capabilities in penetration testing and ensuring robust protection for critical digital assets.
WARNING: This tool is provided for authorized security testing and educational purposes only. Deploying on systems without explicit written authorization violates applicable computer fraud laws (CFAA, CMA, StGB §202a, etc.) and may result in criminal prosecution. The user assumes full responsibility for compliance with all applicable laws.