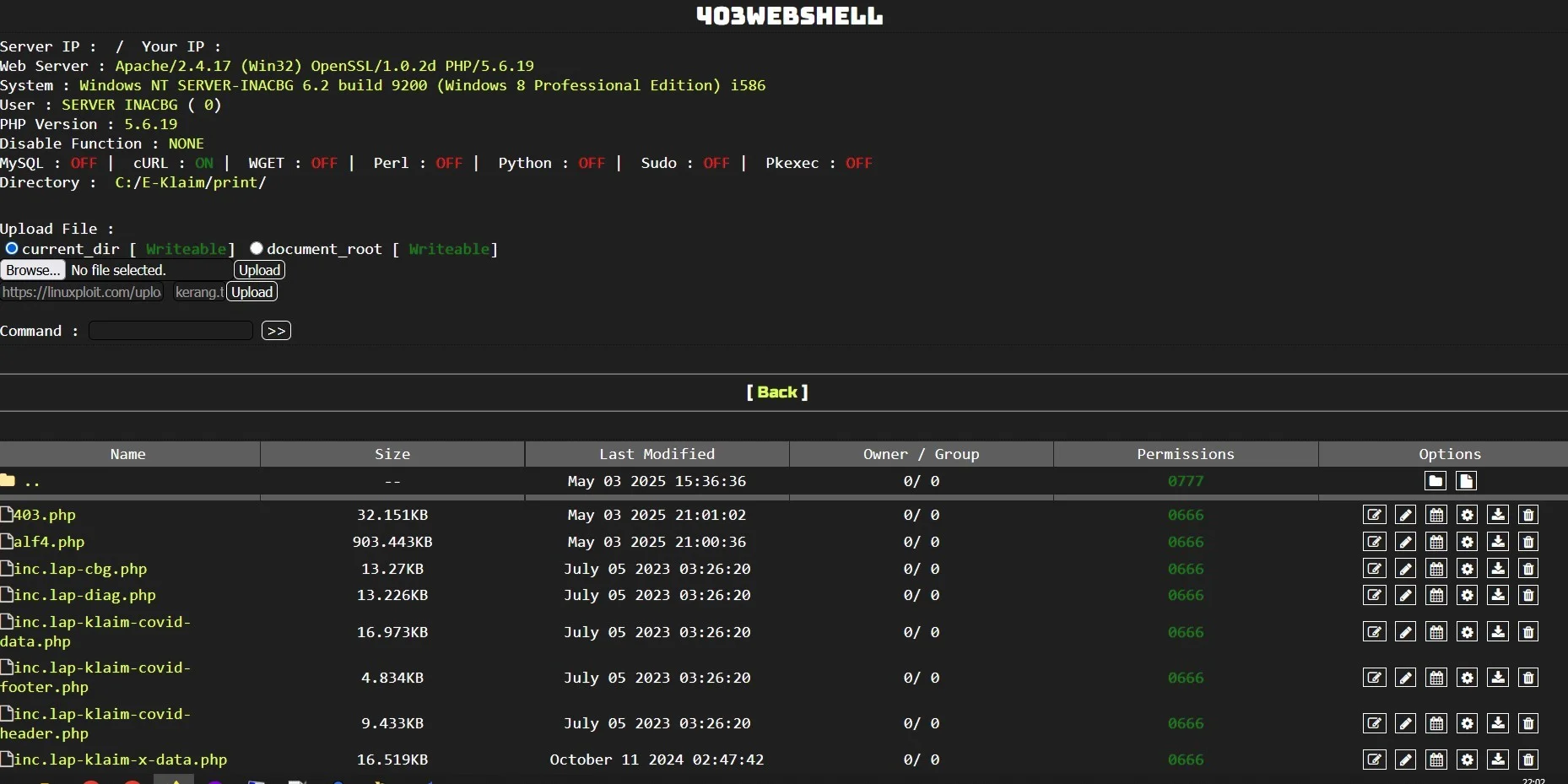
403WebShell Bypass
PHP Shell'403WebShell Bypass' is a PHP web shell tool designed for penetration testing and security auditing, enabling users to bypass server restrictions effectively. Ideal for authorized cybersecurity assessments, it enhances testing precision and access capabilities.
Features
About 403WebShell Bypass
The 403WebShell Bypass is a sophisticated PHP web shell instrument, designed specifically for backend server management and penetration testing. This tool facilitates bypass techniques that enable remote execution through security layers that typically block unauthorized access, thus making it an indispensable resource in ethical hacking and vulnerability assessment. Its core function revolves around simulating attacks on web servers to identify potential security flaws, thereby aiding in comprehensive security auditing. The architecture of 403WebShell Bypass is streamlined for seamless integration and manipulation of server responses, which is critical in environments where stringent web permissions often hinder routine penetration testing tasks. With its ability to mimic legitimate user behavior, it can bypass common security protocols like the HTTP 403 status code, which normally indicates forbidden access. This capability not only enhances the scope of security testing but also equips cybersecurity professionals with a realistic framework to better understand and fortify the defenses of the systems they are tasked to protect. By leveraging such advanced tools, cybersecurity experts can ensure that their assessments accurately reflect the evolving landscape of cyber threats, thereby contributing significantly to the robustness and resilience of IT infrastructures in various organizational contexts.
WARNING: This tool is provided for authorized security testing and educational purposes only. Deploying on systems without explicit written authorization violates applicable computer fraud laws (CFAA, CMA, StGB §202a, etc.) and may result in criminal prosecution. The user assumes full responsibility for compliance with all applicable laws.