IndoXploit Shell v3
PHP ShellIndoXploit Shell v3 is a PHP web shell designed for penetration testing and security auditing, enabling users to bypass server securities efficiently. Ideal for authorized cybersecurity assessments, it offers advanced functionality for exploring vulnerabilities.
Features
About IndoXploit Shell v3
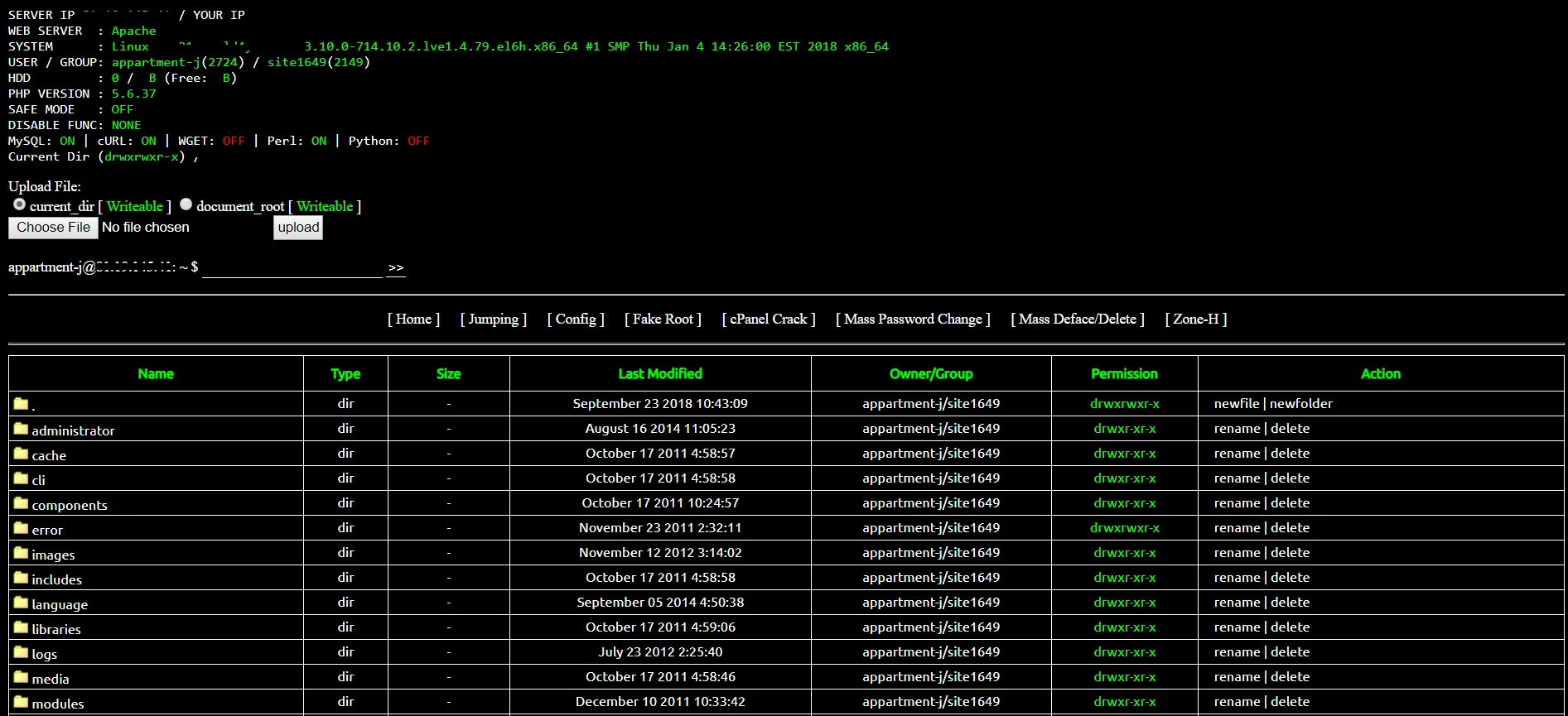
The IndoXploit Shell v3 is a potent PHP web shell tool primarily designed to facilitate backend server management and execute remote commands, which can be invaluable in penetration testing and security auditing. This advanced tool offers a comprehensive suite of functionalities that aids ethical hackers and cybersecurity professionals in conducting thorough vulnerability assessments of web servers. One of the key features of IndoXploit Shell v3 is its ability to bypass certain security protocols, allowing testers to simulate various cybersecurity attacks and identify potential weaknesses within a system. Moreover, its user-friendly interface simplifies the complex process of managing server files and executing server-side scripts, enhancing the efficiency of ethical hacking exercises. The tool is also equipped with robust features for remote execution, which can be crucial in testing how external commands can affect the integrity and performance of the server. By leveraging IndoXploit Shell v3, cybersecurity experts can ensure they conduct their penetration testing and ethical hacking operations within a controlled and secure environment, thereby preemptively identifying and mitigating risks that could compromise the server's security. This web shell is strictly intended for use in authorized security environments and should always be employed with the utmost consideration of legal and ethical standards.
WARNING: This tool is provided for authorized security testing and educational purposes only. Deploying on systems without explicit written authorization violates applicable computer fraud laws (CFAA, CMA, StGB §202a, etc.) and may result in criminal prosecution. The user assumes full responsibility for compliance with all applicable laws.