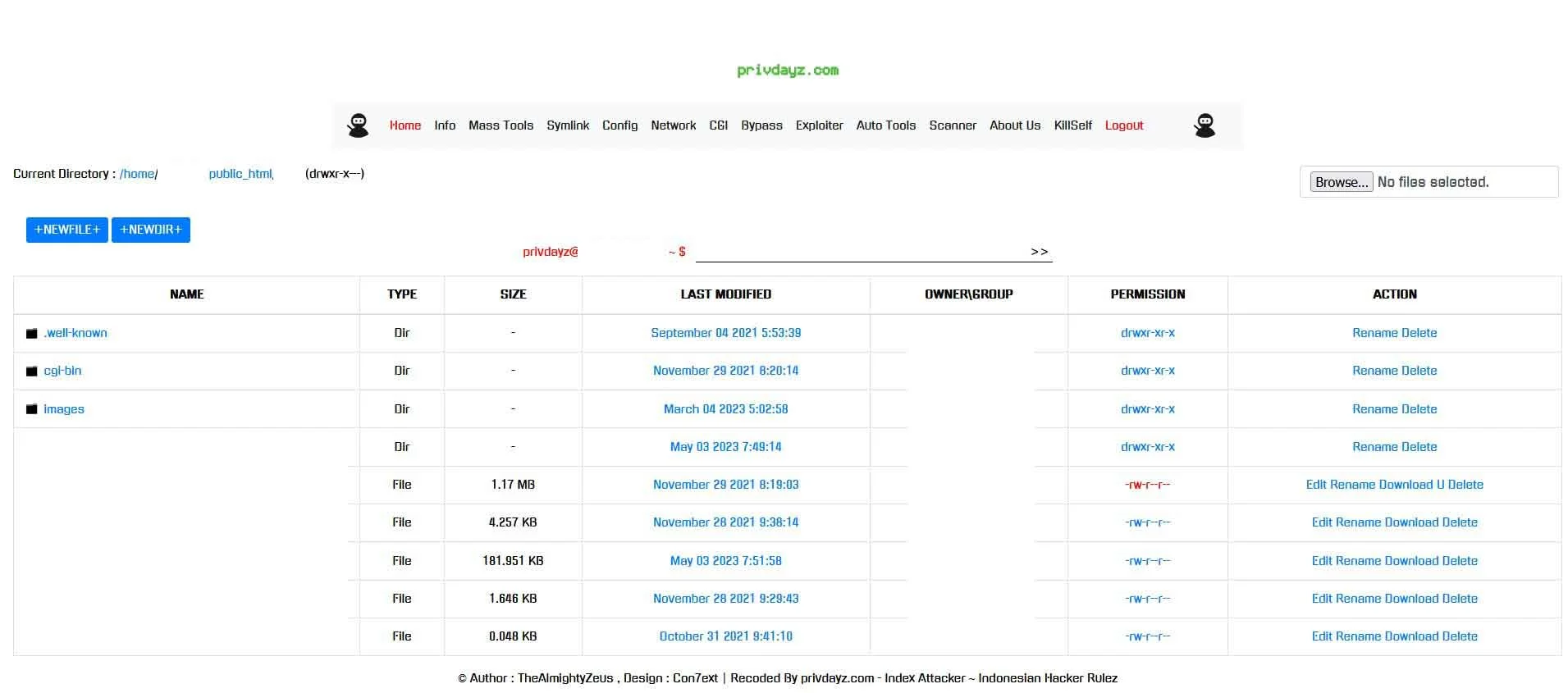
index attacker symlink bypass 404 shell
PHP Shell'Index Attacker Symlink Bypass 404 Shell' is a PHP web shell designed for security auditing and penetration testing, enabling users to bypass symlink restrictions efficiently. This tool is pivotal for authorized vulnerability assessment and defensive cybersecurity strategy enhancement.
Features
About index attacker symlink bypass 404 shell
The PHP web shell tool named 'index attacker symlink bypass 404 shell' is specifically engineered for cybersecurity professionals focusing on backend server management, penetration testing, and security auditing. This intricate tool allows ethical hackers to simulate attack scenarios that exploit vulnerabilities in web server configurations, primarily testing for symlink bypass opportunities and unauthorized 404 error manipulations. What sets this tool apart is its ability to seamlessly integrate within a PHP environment, offering a user-friendly interface that simplifies complex bypass techniques. It is designed to aid in comprehensive vulnerability assessments by enabling remote execution of commands, which is crucial for testing the robustness of server security against intrusion attempts. Ethical hackers utilize such tools to identify and rectify security flaws, thus enhancing the overall security posture of digital assets. The architecture of 'index attacker symlink bypass 404 shell' offers a unique approach to understanding how attackers can leverage unpatched loopholes to gain unauthorized access and how such breaches can be systematically blocked. This tool is a pivotal asset in the arsenal of penetration testers and security professionals aiming to uphold stringent security standards through proactive identification and mitigation of potential threats. Its application, however, is strictly governed under ethical hacking guidelines to ensure that all testing is authorized and intended to improve security measures without any malicious intent.
WARNING: This tool is provided for authorized security testing and educational purposes only. Deploying on systems without explicit written authorization violates applicable computer fraud laws (CFAA, CMA, StGB §202a, etc.) and may result in criminal prosecution. The user assumes full responsibility for compliance with all applicable laws.