Alfa Shell 4.1 Decoded Version
Bypass ShellAlfa Shell 4.1 Decoded Version is a robust PHP web shell designed for penetration testing and security auditing, enabling users to bypass standard access controls effectively. Ideal for secure environment testing and educational purposes.
Features
About Alfa Shell 4.1 Decoded Version
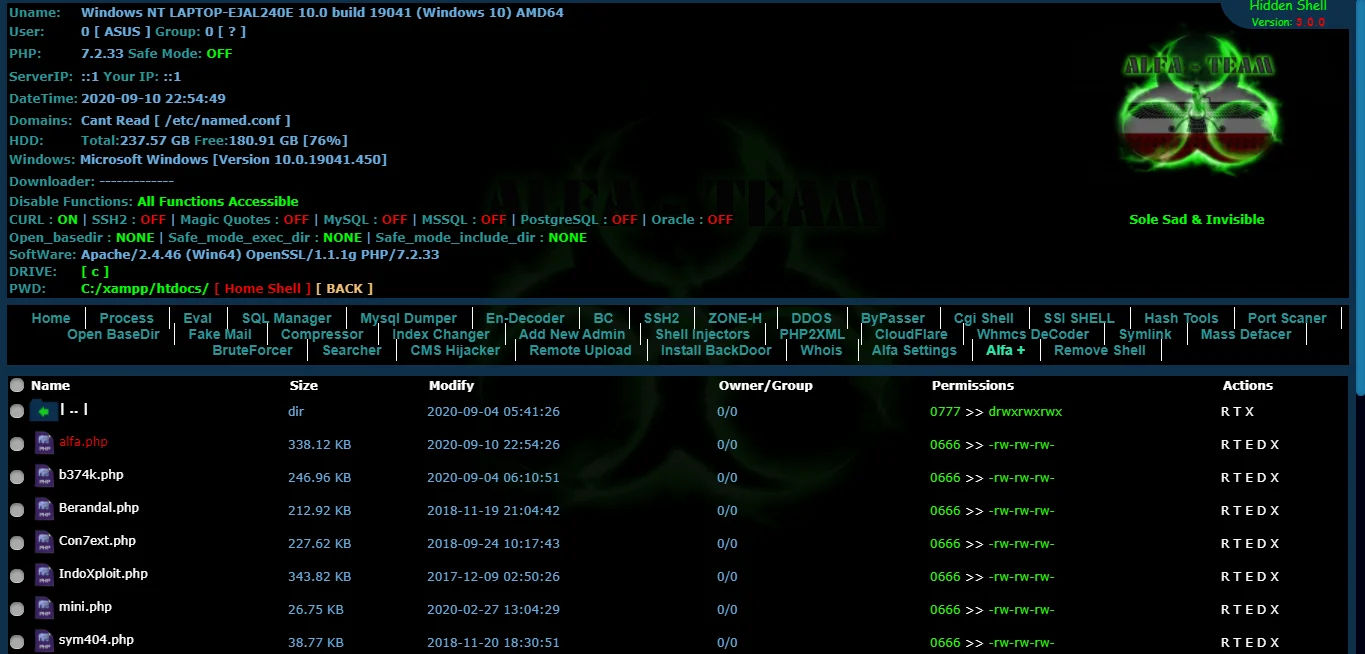
The Alfa Shell 4.1 Decoded Version is a PHP web shell tool extensively used in penetration testing and security auditing to evaluate the security of web servers. As a robust server management script, it facilitates backend server management, allowing testers and ethical hackers to simulate various cyber attack scenarios to assess system vulnerabilities effectively. This tool is particularly useful in demonstrating remote execution capabilities and exploring bypass techniques that cyber attackers might use to exploit weaknesses in web applications. With its decoded nature, Alfa Shell 4.1 offers transparency in its operations, making it easier for security professionals to understand its framework and potentially tailor it to specific vulnerability assessment needs. The tool supports a range of functions from file management to database manipulation, thereby serving as a comprehensive utility for controlled testing environments. It's crucial to emphasize that while Alfa Shell 4.1 can be a potent component in a cybersecurity toolkit, it should only be used within the bounds of legal and ethical guidelines, strictly for educational purposes or authorized security testing. Its capabilities, if misused, can lead to significant security breaches, underscoring the importance of responsible usage in protecting digital assets against unauthorized access and ensuring the integrity of information systems.
WARNING: This tool is provided for authorized security testing and educational purposes only. Deploying on systems without explicit written authorization violates applicable computer fraud laws (CFAA, CMA, StGB §202a, etc.) and may result in criminal prosecution. The user assumes full responsibility for compliance with all applicable laws.